Know Everything
Unlock the power of your network with actionable network and asset intelligence
Improve Uptime
Proactively monitor the health of every network element and port with real-time granular telemetry analysis
Enhance Security
Easily identify potential threats and isolate compromised or at-risk devices
Streamline Operations
Reduce the time and effort required to maintain your network, improve troubleshooting, and ensure compliance
Simplify Deployment
Single solution for critical infrastructure with agentless microsegmentation, secure access, and asset intelligence
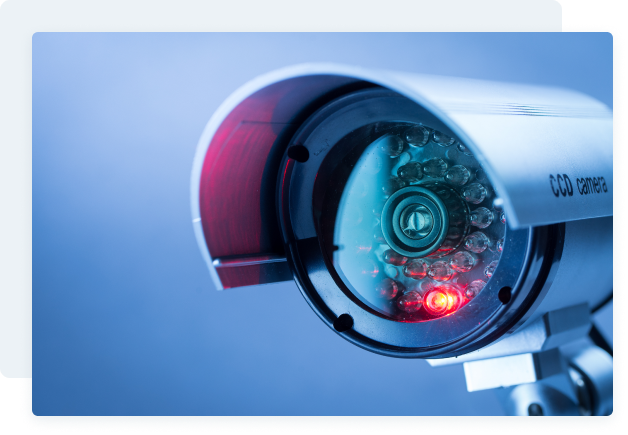
Know What to Protect
Discover every device, every port, every vulnerability. Securely identify all assets in your environment without exposing them to external threats.
Respond Instantly
Airgap asset intelligence provides real-time detection of devices on the network, enabling faster identification and response to potential incidents. Fully integrated with Ransomware Kill Switch™ for complete containment.
Maintain Accuracy
Accurately identify all assets in your network for improved security posture. Ensure regulatory compliance with comprehensive and precise asset inventory. Reduce false positives and minimize incident response times with highly accurate asset intelligence.


